In April 2024, the Core Atlantis Team launched an anonymous survey to better understand our community's needs and help prioritize our roadmap.
If you're an Atlantis user, please take 5 minutes to fill it out: Survey Link
In April 2024, the Core Atlantis Team launched an anonymous survey to better understand our community's needs and help prioritize our roadmap.
If you're an Atlantis user, please take 5 minutes to fill it out: Survey Link
Atlantis supports running server-side conftest policies against the plan output. Common usecases for using this step include:
Enabling "policy checking" in addition to the mergeable apply requirement blocks applies on plans that fail any of the defined conftest policies.
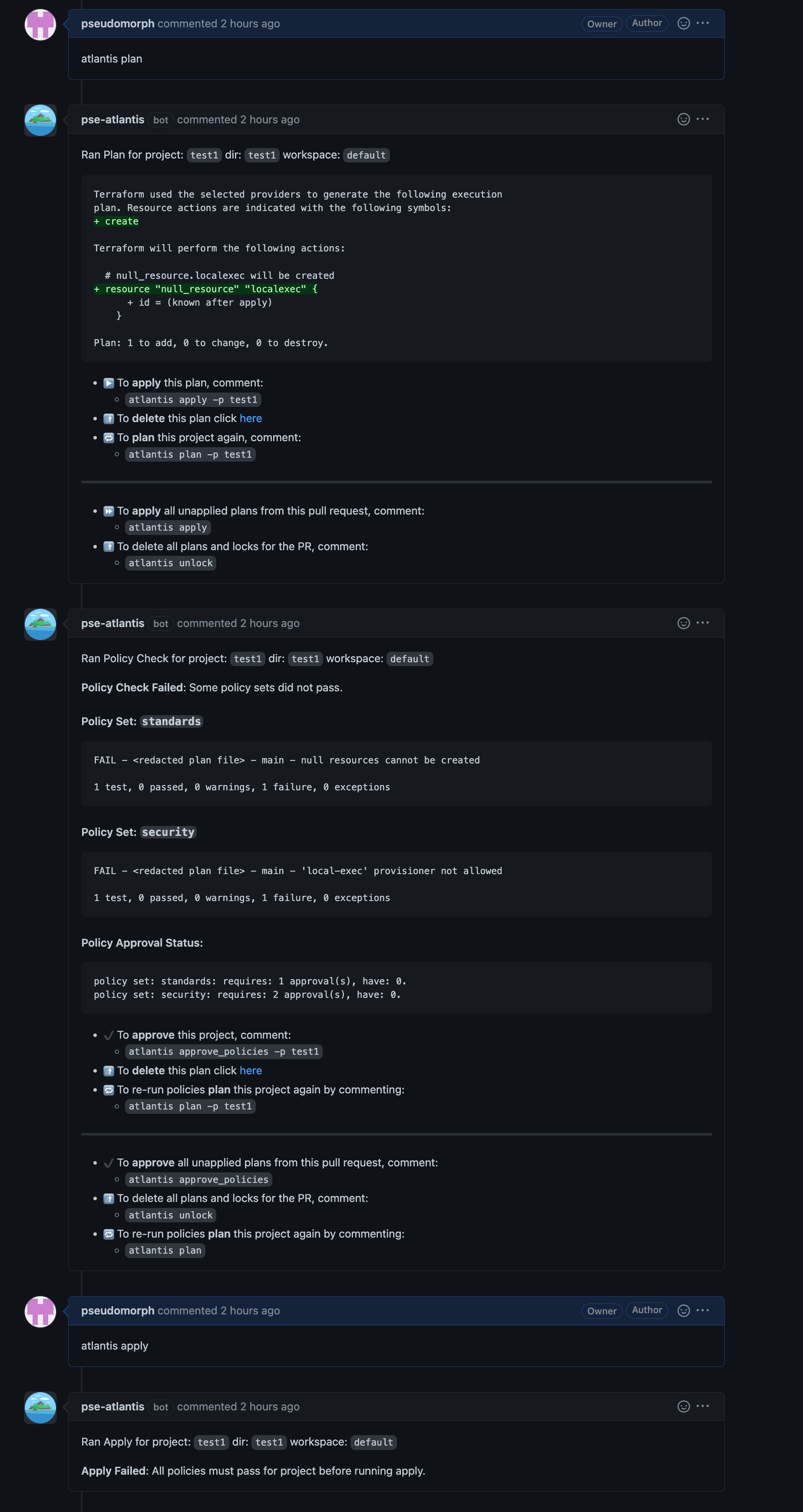
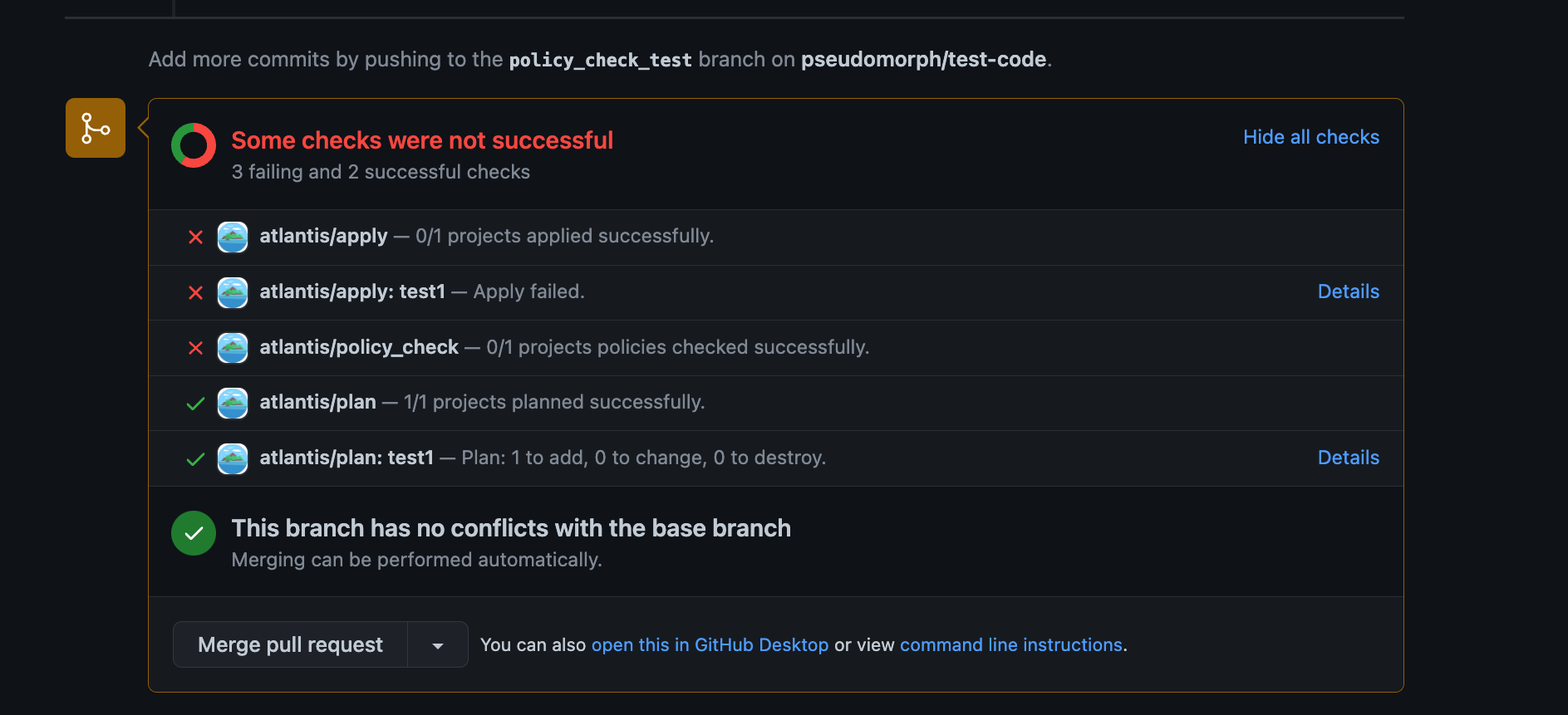
Any failures need to either be addressed in a successive commit, or approved by top-level owner(s) of policies or the owner(s) of the policy set in question. Policy approvals are independent of the approval apply requirement which can coexist in the policy checking workflow. After policies are approved, the apply can proceed.
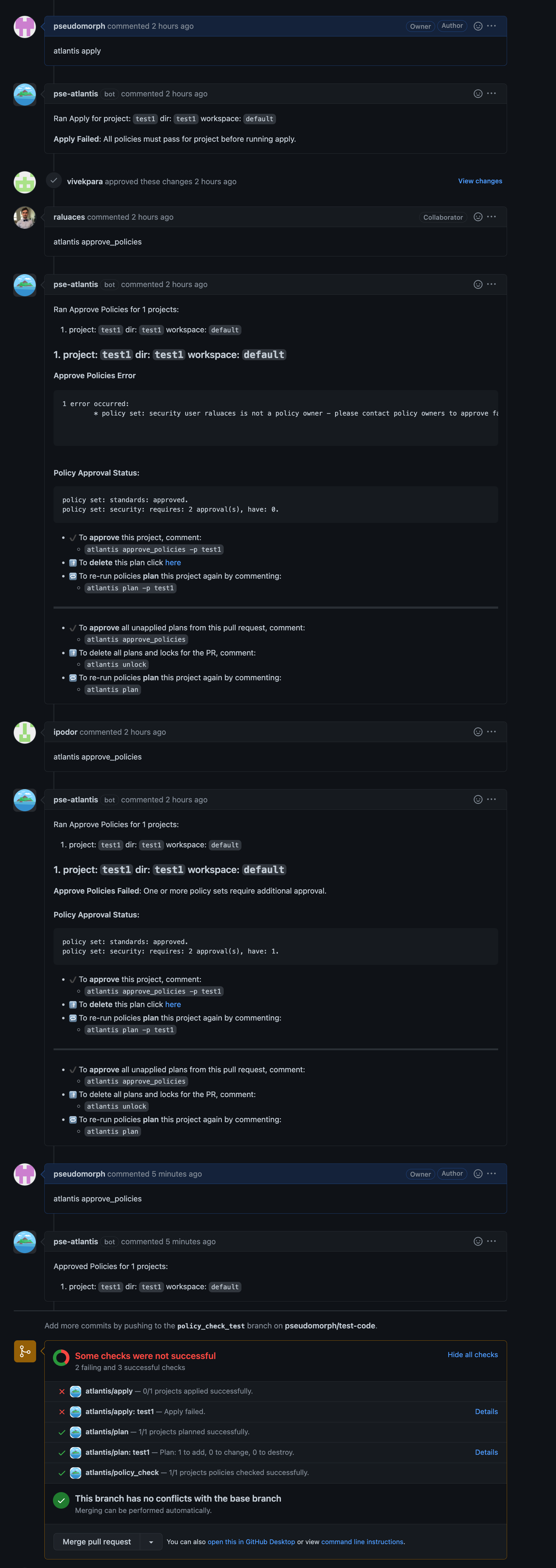
Policy approvals may be cleared either by re-planing, or by issuing the following command:
atlantis approve_policies --clear-policy-approvalWARNING
Any plans following the approval will discard any policy approval and prompt again for it.
This section will provide a guide on how to get set up with a simple policy that fails creation of null_resource's and requires approval from a blessed user.
Enable the workflow using the following server configuration flag --enable-policy-checks
WARNING
All repositories will have policy checking enabled.
Policy Configuration is defined in the server-side repo configuration.
In this example we will define one policy set with one owner:
policies:
owners:
users:
- nishkrishnan
policy_sets:
- name: deny_null_resource
path: <CODE_DIRECTORY>/policies/deny_null_resource/
source: local
- name: deny_local_exec
path: <CODE_DIRECTORY>/policies/deny_local_exec/
source: local
approve_count: 2
owners:
users:
- pseudomorphname - A name of your policy set.path - Path to a policies directory. Note: replace <CODE_DIRECTORY> with absolute dir path to conftest policy/policies.source - Tells atlantis where to fetch the policies from. Currently you can only host policies locally by using local.owners - Defines the users/teams which are able to approve a specific policy set.approve_count - Defines the number of approvals needed to bypass policy checks. Defaults to the top-level policies configuration, if not specified.By default conftest is configured to only run the main package. If you wish to run specific/multiple policies consider passing --namespace or --all-namespaces to conftest with extra_args via a custom workflow as shown in the below example.
Example Server Side Repo configuration using --all-namespaces and a local src dir.
repos:
- id: github.com/myorg/example-repo
workflow: custom
policies:
owners:
users:
- example-dev
policy_sets:
- name: example-conf-tests
path: /home/atlantis/conftest_policies # Consider separate vcs & mount into container
source: local
workflows:
custom:
plan:
steps:
- init
- plan
policy_check:
steps:
- policy_check:
extra_args: ["-p /home/atlantis/conftest_policies/", "--all-namespaces"]Conftest policies are based on Open Policy Agent (OPA) and written in rego. Following our example, simply create a rego file in null_resource_warning folder with following code, the code below a simple policy that will fail for plans containing newly created null_resources.
package main
resource_types = {"null_resource"}
# all resources
resources[resource_type] = all {
some resource_type
resource_types[resource_type]
all := [name |
name:= input.resource_changes[_]
name.type == resource_type
]
}
# number of creations of resources of a given type
num_creates[resource_type] = num {
some resource_type
resource_types[resource_type]
all := resources[resource_type]
creates := [res | res:= all[_]; res.change.actions[_] == "create"]
num := count(creates)
}
deny[msg] {
num_resources := num_creates["null_resource"]
num_resources > 0
msg := "null resources cannot be created"
}That's it! Now your Atlantis instance is configured to run policies on your Terraform plans 🎉
Conftest supports pulling policies from remote locations such as S3, git, OCI, and other protocols supported by the go-getter library. The key extra_args can be used to pass in the --update flag to tell conftest to pull the policies into the project folder before running the policy check.
workflows:
custom:
plan:
steps:
- init
- plan
policy_check:
steps:
- policy_check:
extra_args: ["--update", "s3::https://s3.amazonaws.com/bucket/foo"]Note that authentication may need to be configured separately if pulling policies from sources that require it. For example, to pull policies from an S3 bucket, Atlantis host can be configured with a default AWS profile that has permission to s3:GetObject and s3:ListBucket from the S3 bucket.
By default, Atlantis runs the policy check against the SHOWFILE. In order to run the policy test against Terraform files directly, override the default conftest command used and pass in *.tf as one of the inputs to conftest. The show step is required so that Atlantis will generate the SHOWFILE.
workflows:
custom:
policy_check:
steps:
- show
- run: conftest test $SHOWFILE *.tfBy default, Atlantis will add a comment to all pull requests with the policy check result - both successes and failures. Version 0.21.0 added the --quiet-policy-checks option, which will instead only add comments when policy checks fail, significantly reducing the number of comments when most policy check results succeed.
When the policy check workflow runs, a file is created in the working directory which contains information about the status of each policy set tested. This data may be useful in custom run steps to generate metrics or notifications. The file contains JSON data in the following format:
[
{
"PolicySetName": "policy1",
"PolicyOutput": "",
"Passed": false,
"ReqApprovals": 1,
"CurApprovals": 0
}
]When policy checking is enabled it will be enforced on all repositories, in order to disable policy checking on some repositories first enable policy checks and then disable it explicitly on each repository with the policy_check flag.
For server side config:
# repos.yaml
repos:
- id: /.*/
plan_requirements: [approved]
apply_requirements: [approved]
import_requirements: [approved]
- id: /special-repo/
plan_requirements: [approved]
apply_requirements: [approved]
import_requirements: [approved]
policy_check: falseFor repo level atlantis.yaml config:
version: 3
projects:
- dir: project1
workspace: staging
- dir: project1
workspace: production
policy_check: false